Avast Antivirus Activation Key 2012



AVAST Software leads the security software industry – protecting 131,723,971 active and 166,235,486 registered users around the globe – by distributing FREE antivirus software that makes no compromises in terms of protection. Dependable and fast, with a small resource footprint, it often outperforms competitors paid-for antivirus suites.
Avast Antivirus License Key: W5811254R999701166-5MEBN9P6
This license key also works with the previous versions of Avast Antivirus and will activate them till 2038.Note: This is a free license key and will only work with the free version of Avast Anitvirus. This is NOT valid for the paid version. Download Avast Antivirus Free Version here.
You can also download the VPS virus database for those who are not always connected to the internet by clicking here and installing on your various pc systems.
Remember to share this with your friends and family.
UPDATE
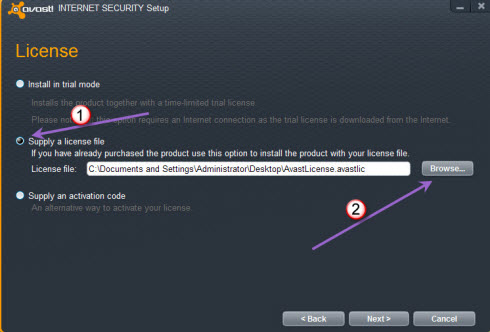
I should have done this a while ago, but I really have been out of blogging. The above key works effectively on all Avast versions on Windows 7 ONLY. However, to effectively install:
Download an Old version of Avast – I would recommend clicking HERE to download.
Insert the Key as you will normally offline.
Get back online and update the Avast software to the most recent. This procedure usually takes a while based on internet speed and size of file.
That s all it takes. Remember it does not work on Windows 8. Will test on Windows 10.
Good luck on the process and as always remember to share with family and friends.
34.528455
69.171703
Like this:
Like Loading
Related
Tagged: Antivirus, Avast, Avast Antivirus, Malicious Software, Microsoft Windows, Product key, Security.
- Hey, Thank you for share avast antivirus. Avast 2014 is latest version of avast antivirus released on 22 January 2014. You should download serial avast 2014 to.
- // How To Use // Install avast. Free Antivirus in trial mode; Open Avast/Maintenance/Registration/Offline registration, Click Insert the license key.
- Protect your devices with the best free antivirus on the market. Download Avast antivirus and anti-spyware protection for your PC, Mac and Android.
Avast Antivirus 2013 with one year license key free download Pro v7.0 full version Latest Update.
Oct 23, 2010 Avast. Free Antivirus is a free antivirus software application which provides comprehensive virus protection for users from virus infection, malware attack.
Only Avast has Home Network Security
For the first time ever, you can protect your home network devices, such as routers and wireless devices, from hacker attacks.
More exciting features
Browser Cleanup
Remove annoying browser toolbars or extensions, and restore your hijacked search browser.
Software Updater
Easily update your important software to increase the overall security and condition of your PC.
Remote Assistance
Remote Assistance lets you help or be helped over the Internet.
There s something free for everyone
Free isn t just the price of our security; it s how you feel when your PCs, Androids, and Macs are protected by the most trusted security in the world.
For home
More people choose our PC and Mac security products over any other.
EXPLORE
For mobile
You run your life on your mobile devices. Avast will keep you safe on the go.
NEW
For business
Whether you are an enterprise or a start up, make sure you re covered.
Avast recommends using the FREE Chrome internet browser.
Download Chrome.
Installing hbedv.key and Licensing For Avira Antivirus Premium Security Suite Internet Security 2012, 2014 Or 2015.
1985 Cabbage Patch Dolls Value
Find 1985 cabbage patch doll cricket doll from a vast selection of Antique Dolls. 1985 cabbage patch New listing Vintage 1985 Coleco Cabbage Patch Kid.
How much is a 1985 cabbage patch doll i believe that cabbage patch dolls were first popular in How much is a 1985 Preemie Cabbage Patch Doll still in the box.

Find great deals on Cabbage patch kids 1985 Dolls, including discounts on the. Suggestions. shop by categories. Best prices on Cabbage patch kids 1985 in Dolls.

Cabbage Patch Kids weren t In 1985, a Cabbage Patch doll named Christopher Coleco In Great Outfits 1 With Freckles Cabbage Patch Dolls Lot 3 1978.
How much is a 1985 Cabbage Patch doll 1980 s cabbage patch dolls on on eBay shows that near mint Cabbage Patch dolls from 1985 sold for an.
Collectible – 1985 Cabbage Patch Dolls

Price of Cabbage Patch Dolls; 1985 cabbage patch kids value; how to price cabbage patch kids; price for cabbage patch dolls; Original Cabbage Patch Doll Price;.
Incoming search terms:1985 Cabbage Patch Doll Valuecabbage patch dolls 1985 price1985 cabbage patch kids babies value guidecabbage patch dolls 1985cost of cabbage patch doll in 19851985 cabbage patch dollspriceof a 1985cabbage premee dollcabbage patch dolls value 19851985 cabbage patch doll with plaid dressxavier roberts cabbage patch kids porceline 1985 cost.
1985 cabbage patch doll 1,103 listings VINTAGE COLECO CABBAGE PATCH KIDS TWINS DOLLS 1985 LIMITED EDITION IN BOX ORANGE. 114.99; Buy It Now; 97.
Collectible – 1985 Cabbage Patch Dolls. 1985 Cabbage Patch Doll Value; cabbage patch dolls 1985 price; 1985 cabbage patch kids babies value guide;.
Driver Hp P1005 Windows 8

HP LaserJet 1005 printer driver you can install Go through the download manually before downloading to update you on available HP Laserjet p1005 driver for windows 7;.

The HP Laserjet p1005 Printer drivers free for windows 8, windows 7. These HP LaserJet p1005 drivers are free, works with all windows, toner, cartridge.
Les mando una sugerencia de pasos para instalar la impresora Laserjet P1005 con Windows 8 HP LaserJet P1005; Windows 8 por la falta del driver.

Free drivers for HP LaserJet P1005. Found 17 files for Windows 10, Windows Print and Scan Doctor driver for HP LaserJet P1005 The HP Print and Scan Doctor was.
Hi Alan,
Thank you for posting in Microsoft Community Forums. I understand that you are unable to use the printer on windows 8 computer.
I apologize for the inconvenience, however no need to worry, we are here to help you and guide you in the right direction.
1.What happens when you try to delete the Printer.
2.Do you get any error message when you try to use the printer.
This printer is not compatible with Windows 8.
Check here:
win8 Locale en-us TextSearch HP 2B1005 2Bprinter Type Both CurrentPage 0 TotalPages 1 ShowCriteria 0 SortCriteria Relevance Compatibility Unknown LastRequested 14
Method 1
Follow these steps and run a Hardware and Devices troubleshooter. Check if the issue gets resolved.
Follow these steps and run the hardware and devices troubleshooter.
a Press Windows Key R, type Control Panel, hit Enter.
b Type Troubleshooting in the search box and select troubleshooting.
c Click on Hardware and Devices troubleshooter.
d Follow the On Screen steps and check if it helps.
Method 2
Outdated printer drivers can cause problems. You may refer to the computer manufacture website and try installing the latest version of printer drivers.
If Windows 8 drivers are not available, then you may install Windows 7 drivers in compatibility mode and check.
a Visit manufacture website and download the drivers on the computer.
b Right click on the driver setup file and select Properties.
c Click the compatibility tab, tick the box next to Run this program in compatibility mode for and select Windows 7.
d In the list-down box; then try installing the device driver via Run as administrator.
To uninstall the printer refer the step below.
I would suggest you to uninstall printer drivers from Device Manager.
a. Press Windows Key R, type devmgmt.msc.
b. Expand the Printer drivers, click on the drivers which you want to uninstall.
c. Click on properties, click on uninstall tab.
d. Click OK.
Let us know the status of the issue. If you need further assistance I will be more than happy to help you.
Regards,
Anil
Be the first person to mark this helpful
i saw this at hp update site:
HP is committed to providing the best product experience for the Windows 8 operating system.
Today, a solution for your printer is not available for Windows 8. However, a driver update will be available in late 2012.
HP aspires to provide the most up-to-date information on HP drivers and software. Please check back for updates.
so we have to wait or change printer. i use at my office so many paper works waits on the que
grrr :
I tried to do it with both programs: ljP1000_P1500-HB-pnp-win64-en.exe and ljP1000_P1500-HB-pnp-win32-en.exe. I tried in both programs by rightclick and then resolve compatibility problems, choose the progam works in an older version and can t be executed
now . Then choose Windows XP service Pack 3. Than I pushed the button test program, after a while I received the message that the program can t be executed,, the printer software installer does not work.
Problem not solved.
Georges Kuster
1 person found this helpful
Answer
DANGER.. SOS.. MAYDAY MAYDAY
I ran the programlink:
br lc pt dlc pt softwareitem bi-54963-6
More than 100Mbyte was downloaded. When I ran the exe the installation of the printer started, but failed. BUT after 2 days I disvovered that met C-drive was renamed with a named I could recogniszed to be linked to the above program. In a first attempt I couldn t
rename it back. First I had to delete all files I could link to HP, after that I could rename my C-drive. At the end I was reassured, oufoef but it took me several hours to discover the solution. So down t make the same attempt as I did
1 person found this helpful.
Free HP LaserJet P1005 drivers for Windows 8. Found 3 files. Select driver to download.


hp 1005 printer on windows 8
- HP LaserJet P1005 Printer Installing Printer Software for a USB Connection in Windows 8 for the HP LaserJet P1005, P1006, P1007, Driver/device description;.
- HP LASERJET P1005 Driver Utility - Windows 8 Downloads - Free Windows8 Download.
- HP Laserjet P1005 Driver Downloads for Microsoft Windows and Macintosh Operating System.
- Use the links on this page to download the latest version of HP LaserJet P1005 drivers. All drivers available for download have been scanned by antivirus program.
Fence Post Driver Ebay
I know there are some of you out there that are gizmo freaks like me, always got to have the new toys. Well years ago, I bought my first Skidril Gas Driven Post.
Post driver, naked lady, fencing tool
40.00
Buy it now
or Best Offer
Great tool, well loved, sad to see it go but no longer fencing. Post stomper, ideal for erecting agricultural fences but useful for anyone gardener who needs to drive in posts. SMALL FENCE POST DRIVER, SLAMMER, THUMPER
The slammer. Put your fence posts in the safe and easy way. 3.5mm thick tubular steel. 680mm long x 108mm internal diameter. solid bar handles. bright red powder coated finish. 10mm thick end capLARGE FENCE POST DRIVER, SLAMMER, THUMPER
The slammer. Small fence post driver. Put your fence posts in the safe and easy way. 3.5mm thick tubular steel. 690mm long x 161mm internal diameter. solid bar handles. Post Driver Knocker Banger Post Cap Fencing
330.00
Free P P
The Post Cap has been fitted with two sliders one on each side to fit on to the mask 8x4 RHS / I-Beam while allowing the mask free movement through the Post Cap and therefore it remains on the Pos.
To order by credit card, call 1-800-639-4099, or click Order to order online with check/money order or via PayPal. WHEATHEART POST DRIVER FOR SALE.
Find great deals on eBay for post driver post rammer. Shop with confidence.

To order by credit card, call 1-800-639-4099, or click Order to order online with check/money order or via PayPal. POST DRIVER LOWES.
Find great deals on eBay for wood fence post treated fence post. Shop with confidence.
Find great deals on eBay for fence post driver hydraulic post driver. Shop with confidence.
Find great deals on eBay for fence post driver post knocker. Shop with confidence.

How much a fence post should cost. Average costs and comments from CostHelper s team of professional journalists and community of users. Posts of weather-resistant.
Site E-studio 450 Driver
HP Toners Printer Cartridges Specialist: Carries complete HP laser printer toner cartridges and other popular printer toner cartridges such as Dell Toner, Xerox.
Support, documentation and driver software–it s all here. Weve made it easier than ever to find exactly what you need. Search for Drivers and Material Safety Data.
Under this entry Toshiba s PPD files for their PostScript printers are hosted. PostScript printers are supported natively in Linux and Unix environments, so.
Generic Postscript driver. Generally, for Postscript printers, you will not need a driver, as all applications produce PostScript. For the printing system.

Hello. everyone.. i m interesting learn in basic how to do a network setup for TOSHIBA e-STUDIO.. Any input will be really appreciated.
Company. Founded in 1999 and headquartered in Irvine, California, Toshiba America Business Solutions TABS is all about helping you manage communications from.
Free fax, copier, and printer repair, support, service, and replacement articles designed to help people find easy solutions to their office equipment problems.
Home Toshiba eSTUDIO 450 Toshiba eSTUDIO 450 Driver
Do you own this machine. Why Not leave a review.
Rating
Name
Comment
Welcome to the Top4Office driver download page for the Toshiba eSTUDIO 450. Below you ll find a selection of drivers available for the Toshiba eSTUDIO 450 machine.
In circumstances where the desired driver is unavailable please feel to contact us at drivers top4office and we ll do our best to find the correct Toshiba eSTUDIO 450 driver for you.
Toshiba eSTUDIO450 Microsoft Windows Drivers
View the Toshiba eSTUDIO 450
SIMILAR
Sharp MX-M160D
758.00
Free Delivery
Toshiba eSTUDIO 195
563.00
Brother DCP-7055
120.00
Toshiba eSTUDIO 203SD plus ADF
520.00
Special Offers
Canon iR1020
1137.60
422.00 VAT
Save 63
Canon MF8180C
785.00
419.99 VAT
Save 46.
We'll contact you.
Problem Abstract This document contains information on the capabilities that are supported on printer hardware from Toshiba. It also indicates whether each printer.
System Error.
Let our experts contact you regarding business solutions and products. Please complete the form below:
First Name
Last Name
Company
Zip Code
Phone Number
Email Address.
Antivirus In The 1980s
Firewalls and Internet Security, the Second Hundred Internet Years by Frederic Avolio, Avolio Consulting Interest and knowledge about computer and network security.

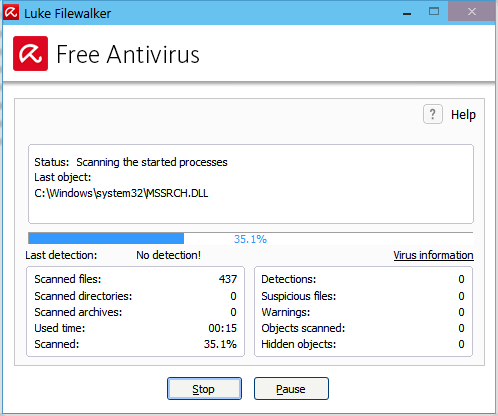
Antivirus or anti-virus software usually written with the acronym of AV is software used to prevent, detect and remove malware of all descriptions, such as: computer viruses, malicious BHOs, hijackers, ransomware, keyloggers, backdoors, rootkits, trojan horses, worms, malicious LSPs, dialers, fraudtools, adware and spyware. Computer security, including protection from social engineering techniques, is commonly offered in products and services of antivirus software companies. This page discusses the software used for the prevention and removal of malware threats, rather than computer security implemented by software methods.
A variety of strategies are typically employed. Signature-based detection involves searching for known patterns of data within executable code. However, it is possible for a computer to be infected with new malware for which no signature is yet known. To counter such so-called zero-day threats, heuristics can be used. One type of heuristic approach, generic signatures, can identify new viruses or variants of existing viruses by looking for known malicious code, or slight variations of such code, in files. Some antivirus software can also predict what a file will do by running it in a sandbox and analyzing what it does to see if it performs any malicious actions.
No matter how useful antivirus software can be, it can sometimes have drawbacks. Antivirus software can impair a computer s performance. Inexperienced users may also have problems understanding the prompts and decisions that antivirus software presents them with. An incorrect decision may lead to a security breach. If the antivirus software employs heuristic detection, success depends on achieving the right balance between false positives and false negatives. False positives can be as destructive as false negatives. 1 Finally, antivirus software generally runs at the highly trusted kernel level of the operating system, creating a potential avenue of attack. 2
History edit
An example of free antivirus software: ClamTk 3.08.
Most of the computer viruses written in the early and mid-1980s were limited to self-reproduction and had no specific damage routine built into the code. 3 That changed when more and more programmers became acquainted with virus programming and created viruses that manipulated or even destroyed data on infected computers.
There are competing claims for the innovator of the first antivirus product. Possibly the first publicly documented removal of a computer virus in the wild was performed by Bernd Fix in 1987. 4 5 There were also two antivirus applications for the Atari ST platform developed in 1987. The first one was G Data 6 and second was UVK 2000. 7
Fred Cohen, who published one of the first academic papers on computer viruses in 1984, 8 began to develop strategies for antivirus software in 1988 9 that were picked up and continued by later antivirus software developers. In 1987, he published a demonstration that there is no algorithm that can perfectly detect all possible viruses. 10
In 1987 the first two heuristic antivirus utilities were released: Flushot Plus by Ross Greenberg and Anti4us by Erwin Lanting. citation needed
Also in 1988 a mailing list named VIRUS-L 11 was started on the BITNET/EARN network where new viruses and the possibilities of detecting and eliminating viruses were discussed. Some members of this mailing list like John McAfee or Eugene Kaspersky later founded software companies that developed and sold commercial antivirus software.
Before internet connectivity was widespread, viruses were typically spread by infected floppy disks. Antivirus software came into use, but was updated relatively infrequently. During this time, virus checkers essentially had to check executable files and the boot sectors of floppy disks and hard disks. However, as internet usage became common, viruses began to spread online. 12
Over the years it has become necessary for antivirus software to check an increasing variety of files, rather than just executables, for several reasons:
Powerful macros used in word processor applications, such as Microsoft Word, presented a risk. Virus writers could use the macros to write viruses embedded within documents. This meant that computers could now also be at risk from infection by opening documents with hidden attached macros. 13
The possibility of embedding executable objects inside otherwise non-executable file formats can make opening those files a risk. 14
Later email programs, in particular Microsoft s Outlook Express and Outlook, were vulnerable to viruses embedded in the email body itself. A user s computer could be infected by just opening or previewing a message. 15
As always-on broadband connections became the norm, and more and more viruses were released, it became essential to update virus checkers more and more frequently. Even then, a new zero-day virus could become widespread before antivirus companies released an update to protect against it.
Identification methods edit
One of the few solid theoretical results in the study of computer viruses is Frederick B. Cohen s 1987 demonstration that there is no algorithm that can perfectly detect all possible viruses. 10
There are several methods which antivirus software can use to identify malware.
Signature based detection is the most common method. To identify viruses and other malware, antivirus software compares the contents of a file to a dictionary of virus signatures. Because viruses can embed themselves in existing files, the entire file is searched, not just as a whole, but also in pieces. 16
Heuristic-based detection, like malicious activity detection, can be used to identify unknown viruses.
File emulation is another heuristic approach. File emulation involves executing a program in a virtual environment and logging what actions the program performs. Depending on the actions logged, the antivirus software can determine if the program is malicious or not and then carry out the appropriate disinfection actions. 17
Signature-based detection edit
Traditionally, antivirus software heavily relied upon signatures to identify malware. This can be very effective, but cannot defend against malware unless samples have already been obtained and signatures created. Because of this, signature-based approaches are not effective against new, unknown viruses.
As new viruses are being created each day, the signature-based detection approach requires frequent updates of the virus signature dictionary. To assist the antivirus software companies, the software may allow the user to upload new viruses or variants to the company, allowing the virus to be analyzed and the signature added to the dictionary. 16
Although the signature-based approach can effectively contain virus outbreaks, virus authors have tried to stay a step ahead of such software by writing oligomorphic, polymorphic and, more recently, metamorphic viruses, which encrypt parts of themselves or otherwise modify themselves as a method of disguise, so as to not match virus signatures in the dictionary. 18
Heuristics edit
Some more sophisticated antivirus software uses heuristic analysis to identify new malware or variants of known malware.
Many viruses start as a single infection and through either mutation or refinements by other attackers, can grow into dozens of slightly different strains, called variants. Generic detection refers to the detection and removal of multiple threats using a single virus definition. 19
For example, the Vundo trojan has several family members, depending on the antivirus vendor s classification. Symantec classifies members of the Vundo family into two distinct categories, Trojan.Vundo and Trojan.Vundo.B. 20 21
While it may be advantageous to identify a specific virus, it can be quicker to detect a virus family through a generic signature or through an inexact match to an existing signature. Virus researchers find common areas that all viruses in a family share uniquely and can thus create a single generic signature. These signatures often contain non-contiguous code, using wildcard characters where differences lie. These wildcards allow the scanner to detect viruses even if they are padded with extra, meaningless code. 22 A detection that uses this method is said to be heuristic detection.
Rootkit detection edit
Anti-virus software can attempt to scan for rootkits; a rootkit is a type of malware that is designed to gain administrative-level control over a computer system without being detected. Rootkits can change how the operating system functions and in some cases can tamper with the anti-virus program and render it ineffective. Rootkits are also difficult to remove, in some cases requiring a complete re-installation of the operating system. 23
Real-time protection edit
Real-time protection, on-access scanning, background guard, resident shield, autoprotect, and other synonyms refer to the automatic protection provided by most antivirus, anti-spyware, and other anti-malware programs. This monitors computer systems for suspicious activity such as computer viruses, spyware, adware, and other malicious objects in real-time, in other words while data loaded into the computer s active memory: when inserting a CD, opening an email, or browsing the web, or when a file already on the computer is opened or executed. 24
Issues of concern edit
Unexpected renewal costs edit
Some commercial antivirus software end-user license agreements include a clause that the subscription will be automatically renewed, and the purchaser s credit card automatically billed, at the renewal time without explicit approval. For example, McAfee requires users to unsubscribe at least 60 days before the expiration of the present subscription 25 while BitDefender sends notifications to unsubscribe 30 days before the renewal. 26 Norton AntiVirus also renews subscriptions automatically by default. 27
Rogue security applications edit
Main article: Rogue security software
Some apparent antivirus programs are actually malware masquerading as legitimate software, such as WinFixer, MS Antivirus, and Mac Defender. 28
Problems caused by false positives edit
A false positive is when antivirus software identifies a non-malicious file as a virus. When this happens, it can cause serious problems. For example, if an antivirus program is configured to immediately delete or quarantine infected files, a false positive in an essential file can render the operating system or some applications unusable. 29 In May 2007, a faulty virus signature issued by Symantec mistakenly removed essential operating system files, leaving thousands of PCs unable to boot. 30 Also in May 2007, the executable file required by Pegasus Mail was falsely detected by Norton AntiVirus as being a Trojan and it was automatically removed, preventing Pegasus Mail from running. Norton AntiVirus had falsely identified three releases of Pegasus Mail as malware, and would delete the Pegasus Mail installer file when that happened. 31 In response to this Pegasus Mail stated:
On the basis that Norton/Symantec has done this for every one of the last three releases of Pegasus Mail, we can only condemn this product as too flawed to use, and recommend in the strongest terms that our users cease using it in favour of alternative, less buggy anti-virus packages. 31
In April 2010, McAfee VirusScan detected svchost.exe, a normal Windows binary, as a virus on machines running Windows XP with Service Pack 3, causing a reboot loop and loss of all network access. 32 33
In December 2010, a faulty update on the AVG anti-virus suite damaged 64-bit versions of Windows 7, rendering it unable to boot, due to an endless boot loop created. 34
In October 2011, Microsoft Security Essentials MSE removed the Google Chrome web browser, rival to Microsoft s own Internet Explorer. MSE flagged Chrome as a Zbot banking trojan. 35
When Microsoft Windows becomes damaged by faulty anti-virus products, fixing the damage to Microsoft Windows incurs technical support costs and businesses can be forced to close whilst remedial action is undertaken. 36 37
System and interoperability related issues edit
Running multiple antivirus programs concurrently can degrade performance and create conflicts. 38 However, using a concept called multiscanning, several companies including G Data 39 and Microsoft 40 have created applications which can run multiple engines concurrently.
It is sometimes necessary to temporarily disable virus protection when installing major updates such as Windows Service Packs or updating graphics card drivers. 41 Active antivirus protection may partially or completely prevent the installation of a major update. Anti-virus software can cause problems during the installation of an operating system upgrade, e.g. when upgrading to a newer version of Windows in place without erasing the previous version of Windows. Microsoft recommends that anti-virus software be disabled to avoid conflicts with the upgrade installation process. 42 43 44
The functionality of a few computer programs can be hampered by active anti-virus software. For example TrueCrypt, a disk encryption program, states on its troubleshooting page that anti-virus programs can conflict with TrueCrypt and cause it to malfunction or operate very slowly. 45 Anti-virus software can impair the performance and stability of games running in the Steam platform. 46
Support issues also exist around antivirus application interoperability with common solutions like SSL VPN remote access and network access control products. 47 These technology solutions often have policy assessment applications which require that an up to date antivirus is installed and running. If the antivirus application is not recognized by the policy assessment, whether because the antivirus application has been updated or because it is not part of the policy assessment library, the user will be unable to connect.
Effectiveness edit
Studies in December 2007 showed that the effectiveness of antivirus software had decreased in the previous year, particularly against unknown or zero day attacks. The computer magazine c t found that detection rates for these threats had dropped from 40-50 in 2006 to 20-30 in 2007. At that time, the only exception was the NOD32 antivirus, which managed a detection rate of 68 percent. 48
The problem is magnified by the changing intent of virus authors. Some years ago it was obvious when a virus infection was present. The viruses of the day, written by amateurs, exhibited destructive behavior or pop-ups. Modern viruses are often written by professionals, financed by criminal organizations. 49
Independent testing on all the major virus scanners consistently shows that none provide 100 virus detection. The best ones provided as high as 99.6 detection, while the lowest provided only 81.8 in tests conducted in February 2010. All virus scanners produce false positive results as well, identifying benign files as malware. 50
Although methodologies may differ, some notable independent quality testing agencies include AV-Comparatives, ICSA Labs, West Coast Labs, Virus Bulletin, AV-TEST and other members of the Anti-Malware Testing Standards Organization. 51 52
New viruses edit
Anti-virus programs are not always effective against new viruses, even those that use non-signature-based methods that should detect new viruses. The reason for this is that the virus designers test their new viruses on the major anti-virus applications to make sure that they are not detected before releasing them into the wild. 53
Some new viruses, particularly ransomware, use polymorphic code to avoid detection by virus scanners. Jerome Segura, a security analyst with ParetoLogic, explained: 54
It s something that they miss a lot of the time because this type of ransomware virus comes from sites that use a polymorphism, which means they basically randomize the file they send you and it gets by well-known antivirus products very easily. I ve seen people firsthand getting infected, having all the pop-ups and yet they have antivirus software running and it s not detecting anything. It actually can be pretty hard to get rid of, as well, and you re never really sure if it s really gone. When we see something like that usually we advise to reinstall the operating system or reinstall backups. 54
A proof of concept virus has used the Graphics Processing Unit GPU to avoid detection from anti-virus software. The potential success of this involves bypassing the CPU in order to make it much harder for security researchers to analyse the inner workings of such malware. 55
Rootkits edit
Detecting rootkits is a major challenge for anti-virus programs. Rootkits have full administrative access to the computer and are invisible to users and hidden from the list of running processes in the task manager. Rootkits can modify the inner workings of the operating system 56 and tamper with antivirus programs.
Damaged files edit
Files which have been damaged by computer viruses are normally damaged beyond recovery. Anti-virus software removes the virus code from the file during disinfection, but this does not always restore the file to its undamaged state. In such circumstances, damaged files can only be restored from existing backups; installed software that is damaged requires re-installation 57 however, see System File Checker.
Firmware issues edit
Active anti-virus software can interfere with a firmware update process. 58 Any writeable firmware in the computer can be infected by malicious code. 59 This is a major concern, as an infected BIOS could require the actual BIOS chip to be replaced to ensure the malicious code is completely removed. 60 Anti-virus software is not effective at protecting firmware and the motherboard BIOS from infection. 61
Other methods edit
A command-line virus scanner, Clam AV 0.95.2, running a virus signature definition update, scanning a file and identifying a Trojan
Installed antivirus software running on an individual computer is only one method of guarding against viruses. Other methods are also used, including cloud-based antivirus, firewalls and on-line scanners.
Cloud antivirus edit
Cloud antivirus is a technology that uses lightweight agent software on the protected computer, while offloading the majority of data analysis to the provider s infrastructure. 62
One approach to implementing cloud antivirus involves scanning suspicious files using multiple antivirus engines. This approach was proposed by an early implementation of the cloud antivirus concept called CloudAV. CloudAV was designed to send programs or documents to a network cloud where multiple antivirus and behavioral detection programs are used simultaneously in order to improve detection rates. Parallel scanning of files using potentially incompatible antivirus scanners is achieved by spawning a virtual machine per detection engine and therefore eliminating any possible issues. CloudAV can also perform retrospective detection, whereby the cloud detection engine rescans all files in its file access history when a new threat is identified thus improving new threat detection speed. Finally, CloudAV is a solution for effective virus scanning on devices that lack the computing power to perform the scans themselves. 63
Some examples of cloud anti-virus products are Panda Cloud Antivirus and Immunet.
Network firewall edit
Network firewalls prevent unknown programs and processes from accessing the system. However, they are not antivirus systems and make no attempt to identify or remove anything. They may protect against infection from outside the protected computer or network, and limit the activity of any malicious software which is present by blocking incoming or outgoing requests on certain TCP/IP ports. A firewall is designed to deal with broader system threats that come from network connections into the system and is not an alternative to a virus protection system.
Online scanning edit
Some antivirus vendors maintain websites with free online scanning capability of the entire computer, critical areas only, local disks, folders or files. Periodic online scanning is a good idea for those that run antivirus applications on their computers because those applications are frequently slow to catch threats. One of the first things that malicious software does in an attack is disable any existing antivirus software and sometimes the only way to know of an attack is by turning to an online resource that is not installed on the infected computer. 64
Specialist tools edit
Using rkhunter to scan for rootkits on an Ubuntu Linux computer.
Virus removal tools are available to help remove stubborn infections or certain types of infection. Examples include Trend Micro s Rootkit Buster, 65 and rkhunter for the detection of rootkits, Avira s AntiVir Removal Tool, 66 PCTools Threat Removal Tool, 67 and AVG s Anti-Virus Free 2011. 68
A rescue disk that is bootable, such as a CD or USB storage device, can be used to run antivirus software outside of the installed operating system, in order to remove infections while they are dormant. A bootable antivirus disk can be useful when, for example, the installed operating system is no longer bootable or has malware that is resisting all attempts to be removed by the installed antivirus software. Examples of some of these bootable disks include the Avira AntiVir Rescue System, 66 PCTools Alternate Operating System Scanner, 69 and AVG Rescue CD. 70 The AVG Rescue CD software can also be installed onto a USB storage device, that is bootable on newer computers. 70
Usage and risks edit
According to an FBI survey, major businesses lose 12 million annually dealing with virus incidents. 71 A survey by Symantec in 2009 found that a third of small to medium sized business did not use antivirus protection at that time, whereas more than 80 of home users had some kind of antivirus installed. 72 According to a sociological survey conducted by G Data Software in 2010 49 of women did not use any antivirus program at all. 73
See also edit
Software portal
Computer security portal
References edit
Softpedia Exclusive Interview: Avira 10. Ionut Ilascu. Softpedia. 14 April 2010. Retrieved 2011-09-11.
Norton AntiVirus ignores malicious WMI instructions. Munir Kotadia. CBS Interactive. 21 October 2004. Retrieved 2009-04-05.
History of viruses
Kaspersky Lab Virus list
Wells, Joe 1996-08-30. Virus timeline. IBM. Archived from the original on 4 June 2008. Retrieved 2008-06-06.
G Data Software AG 2011. G Data presents security firsts at CeBIT 2010. Retrieved 22 August 2011.
Karsmakers, Richard January 2010. The ultimate Virus Killer UVK 2000. Retrieved 22 August 2011.
Fred Cohen 1984 Computer Viruses – Theory and Experiments
Fred Cohen 1988 On the implications of Computer Viruses and Methods of Defense
a b Cohen, Fred, An Undetectable Computer Virus, 1987, IBM
VIRUS-L mailing list archive
Panda Security April 2004. II Evolution of computer viruses. Retrieved 2009-06-20.
Szor 2005, pp. 66–67
New virus travels in PDF files. 7 August 2001. Retrieved 2011-10-29.
Slipstick Systems February 2009. Protecting Microsoft Outlook against Viruses. Archived from the original on 2 June 2009. Retrieved 2009-06-18.
a b Landesman, Mary 2009. What is a Virus Signature.. Retrieved 2009-06-18.
Szor 2005, pp. 474–481
Szor 2005, pp. 252–288
Generic detection. Kaspersky. Retrieved 2009-02-24.
Symantec Corporation February 2009. Trojan.Vundo. Archived from the original on 9 April 2009. Retrieved 2009-04-14.
Symantec Corporation February 2007. Trojan.Vundo.B. Archived from the original on 27 April 2009. Retrieved 2009-04-14.
Antivirus Research and Detection Techniques. ExtremeTech. Archived from the original on 27 February 2009. Retrieved 2009-02-24.
Rootkit
Kaspersky Lab Technical Support Portal Archived 13 February 2011 at WebCite
Kelly, Michael October 2006. Buying Dangerously. Retrieved 2009-11-29.
Bitdefender 2009. Automatic Renewal. Retrieved 2009-11-29.
Symantec undated. Ongoping Protection. Retrieved 2009-11-29.
SpywareWarrior 2007. Rogue/Suspect Anti-Spyware Products Web Sites. Retrieved 2009-11-29.
Emil Protalinski November 11, 2008. AVG incorrectly flags user32.dll in Windows XP SP2/SP3. Ars Technica. Retrieved 2011-02-24.
Aaron Tan May 24, 2007. Flawed Symantec update cripples Chinese PCs. CNET Networks. Retrieved 2009-04-05.
a b David Harris June 29, 2009. January 2010 - Pegasus Mail v4.52 Release. Pegasus Mail. Archived from the original on 28 May 2010. Retrieved 2010-05-21.
McAfee DAT 5958 Update Issues. 21 April 2010. Archived from the original on 24 April 2010. Retrieved 22 April 2010.
Botched McAfee update shutting down corporate XP machines worldwide. 21 April 2010. Archived from the original on 22 April 2010. Retrieved 22 April 2010.
John Leyden December 2, 2010. Horror AVG update ballsup bricks Windows 7. The Register. Retrieved 2010-12-02.
MSE false positive detection forces Google to update Chrome, retrieved Monday, 3 October 2011
McAfee to compensate businesses for buggy update, retrieved Thursday, 2 December 2010
Buggy McAfee update whacks Windows XP PCs, archived from the original on 13 January 2011, retrieved Thursday, 2 December 2010
Microsoft January 2007. Plus. 98: How to Remove McAfee VirusScan. Archived from the original on 11 November 2009. Retrieved 2009-11-29.
Robert Vamosi May 28, 2009. G-Data Internet Security 2010. PC World. Retrieved 2011-02-24.
Kelly Jackson Higgins May 5, 2010. New Microsoft Forefront Software Runs Five Antivirus Vendors Engines. Darkreading. Retrieved 2011-02-24.
Microsoft April 2009. Steps to take before you install Windows XP Service Pack 3. Archived from the original on 8 December 2009. Retrieved 2009-11-29.
Upgrading from Windows Vista to Windows 7. Retrieved 24 March 2012. Mentioned within Before you begin.
Upgrading to Microsoft Windows Vista recommended steps.. Retrieved 24 March 2012.
How to troubleshoot problems during installation when you upgrade from Windows 98 or Windows Millennium Edition to Windows XP. Last Review: May 7, 2007. Retrieved 24 March 2012. Mentioned within General troubleshooting.
Troubleshooting. Retrieved 2011-02-17.
Spyware, Adware, and Viruses Interfering with Steam. Retrieved 11 April 2013. Steam support page.
Field Notice: FN - 63204 - Cisco Clean Access has Interoperability issue with Symantec Anti-virus - delays Agent start-up
Dan Goodin December 21, 2007. Anti-virus protection gets worse. Channel Register. Retrieved 2011-02-24.
Dan Illett July 13, 2007. Hacking poses threats to business. Computer Weekly. Retrieved 2009-11-15.
AV Comparatives February 2010. Anti-Virus Comparative No. 25. Archived from the original on 30 March 2010. Retrieved 18 April 2010.
Guidelines released for antivirus software tests
Harley, David 2011. AVIEN Malware Defense Guide for the Enterprise. Elsevier. p. 487. ISBN 9780080558660. Retrieved 2013-06-10.
Kotadia, Munir July 2006. Why popular antivirus apps do not work. Retrieved 14 April 2010.
a b The Canadian Press April 2010. Internet scam uses adult game to extort cash. CBC News. Archived from the original on 18 April 2010. Retrieved 17 April 2010.
Researchers up evilness ante with GPU-assisted malware - Coming to a PC near you, by Dan Goodin
GIBSON RESEARCH CORPORATION SERIES: Security Now.
How Anti-Virus Software Works. Retrieved 2011-02-16.
BT Home Hub Firmware Upgrade Procedure. Retrieved 2011-03-06.
The 10 faces of computer malware. July 17, 2009. Retrieved 2011-03-06.
New BIOS Virus Withstands HDD Wipes. Friday 27 March 2009. Retrieved 2011-03-06.
Phrack Inc. Persistent BIOS Infection. June 1, 2009. Retrieved 2011-03-06.
Zeltser, Lenny October 2010. What Is Cloud Anti-Virus and How Does It Work.. Archived from the original on 10 October 2010. Retrieved 2010-10-26.
Jon Erickson August 6, 2008. Antivirus Software Heads for the Clouds. Information Week. Retrieved 2010-02-24.
Brian Krebs March 9, 2007. Online Anti-Virus Scans: A Free Second Opinion. Washington Post. Retrieved 2011-02-24.
Ryan Naraine February 2, 2007. Trend Micro ships free rootkit buster. ZDNet. Retrieved 2011-02-24.
a b Neil J. Rubenking March 26, 2010. Avira AntiVir Personal 10. PC Magazine. Retrieved 2011-02-24.
Neil J. Rubenking September 16, 2010. PC Tools Spyware Doctor with AntiVirus 2011. PC Magazine. Retrieved 2011-02-24.
Neil J. Rubenking October 4, 2010. AVG Anti-Virus Free 2011. PC Magazine. Retrieved 2011-02-24.
Neil J. Rubenking November 19, 2009. PC Tools Internet Security 2010. PC Magazine. Retrieved 2011-02-24.
a b Carrie-Ann Skinner March 25, 2010. AVG Offers Free Emergency Boot CD. PC World. Retrieved 2011-02-24.
FBI estimates major companies lose 12m annually from viruses. 30 January 2007. Retrieved 20 February 2011.
Michael Kaiser April 17, 2009. Small and Medium Size Businesses are Vulnerable. National Cyber Security Alliance. Retrieved 2011-02-24.
Nearly 50 of women don t use antivirus. SPAMfighter.
Bibliography edit
External links edit
Antivirus software at the Open Directory Project.
Jan 29, 2013 GEEK TRIVIA. HTG Explains: Why You Don t Need an Antivirus On Linux and When You Do.
- Free Versus Fee Antivirus software is sold or distributed in many forms, from standalone antivirus scanners to complete Internet security suites that bundle antivirus.
- Article explaining what a Computer Virus is, and how it can affect your computer.
- Antivirus or anti-virus software often abbreviated as AV, sometimes known as anti-malware software, is computer software used to prevent, detect and remove.
- Feb 06, 2004 E-mail users who were slow to update their antivirus software last week may have been surprised to receive a flood of e-mail messages containing. zip files.
Top 10 free antivirus, our free antivirus reviews pick all the best free antivirus software available today, we also offer free antivirus download button for our.
Berg Und Tunnelbau Simulator Patch
May 16, 2012 - Berg- und Tunnelbau Simulator – Startprobleme ausgemerzt – Patch bei Gameswelt.
The ultimate source of patches addons for Berg- Tunnelbau Simulator.
Közel húsz éves tapasztalattal állunk a kedves megrendelőink szolgálatába. Megpróbálunk mindig minden igényt kielégíteni, a kért munkát a legprecízebb.
Du hast ein Problem mit Berg- und Tunnelbau Simulator PC oder kommst einfach an einer Kann mir jemand sagen wo ich einen Patch für Berg- cool777.
Berg- Tunnelbau Simulator. Also known as: Mining Tunneling Simulator Belongs to Series: Available on: PC Release date: Patch 1.0.0.1. Download patch 1.0.0.1.
Berg und Tunnelbau Simulator, 1191 records found, first 100 of them are.
CracksNet
Betriebssystem: Windows: XP / Vista / 7
Prozessor: 2GHz
Arbeitsspeicher: 1 GB
Laufwerk: CD-ROM
Sound: 3D-Sound
HD: 750 MB
DirectX: 9 oder höher
Peripherie: Tastatur, Maus
3D Grafikkarte: Geforce 6800 Serie / ATI X1600, S3 C, 430GT min. 128 MB VRAM oder höher, Shader Modell 3.0 oder höher
Patches Updates
Behebt Startprobleme und mehr. Führt eine Autoupdate-Funktion ein, damit spätere Patches direkt über das Spiel geladen werden können. Sobald es Neuheiten gibt, erscheint nach dem Spielstart ein entsprechender Hinweis. Hierzu ist allerdings eine Verbindung zum Internet notwendig. Falls Sie eine Firewall einsetzen, stellen Sie bitte sicher, dass das Spiel auf das Internet zugreifen darf.
Auf einigen Systemen kann es nötig sein, dass Sie das Spiel als Administrator starten Windows Vista oder Windows 7. Hierzu klicken Sie die Spiel-Verknüpfung mit der rechten Maustaste an und wählen aus dem erscheinenden Menü Als Administrator ausführen.
Stand: 04.07.2010, Download: 231 MB
Änderungen:
Autoupdate-Funktion
Behebt Startprobleme.
Führt eine Autoupdate-Funktion ein, damit spätere Patches direkt über das Spiel berg und tunnelbau screen001 berg und tunnelbau screen002 berg und.
Strassenbau Und Meisterei Simulator German-0x0007 serial keys genSpreng -und Abriss Simulator German-bamboocha serial key genStrassenbau Und Meisterei Simulator crackStrassenbau Und Meisterei Simulator German-0x0007 Seeded serial keygenTourist Trophy: The Real Riding Simulator serial number makerGarmin G1000 Flight Simulator serial keygenGeo-political Simulator Gps English serial keygen8085 Simulator serialFarming Simulator 2009 serial number makerKran Simulator 2009 keygenWebcam-simulator 2.159 serial keygenTrainz Simulator 2010 serial keys genApple Iphone Ipad Simulator From 3.2 serials keyShip Simulator 2006 key code generatorCity Bus Simulator 2010 serial key genEye Toy Thomas Und Seine Freunde serials keyMicrosoft Flight Simulator Fsx Vlj Business Jet-skidrow serial number makerForklift Truck Simulator patchGerman Truck Simulator 2009 serial keys genOrbiter Space Flight Simulator 2006 crackUk Truck Simulator serials generatorWinxp Simulator keygenSail Simulator 2010 serialEuro Truck Simulator.exe serial makerGarmin Xt Mobile Mit Anleitung Und Programme West - Europa Karte serials keyFarming.simulator 2009 crackDriving Simulator 2009 keygenPanzer Simulator keymakerRail Simulator-hatred key generatorWebcam-simulator-xp-edition 3.452 serial keygenMicrosoft Flight Simulator X Deluxe serials keyShip Simulator 2008 serial number makerMicrosoft Flight Simulator X.addon Aerosoft Hawaii Dillingham X serials keyWebcam-simulator-xp-edition 3.49 serial makerPc Military Tank Simulator Direct Play -tptb patchFlight Simulator X Add-ons - Military Aircraft crackMicrosoft Flight Simulator 2004 keymaker2206 Bus Simulator 2008 serial keygenGerman.truck.simulator-tinyiso crackWebcam-simulator 2.112 serial number makerRail Simulator Class 66 serials keyMicrosoft Flight Simulator Addon Aerosoft Proflight Emulator Del serial keygenTrain Simulator-german Railroad Vol 1 serial makerShitterman - Bajs Simulator serial keygenCombat Flight Simulator 3 key code generatorEuro Truck Simulator key code generatorGarmin G1000 Simulator serials generatorGabelstapler Simulator 2009 crackGerman Truck Simulator Magyar keymakerSchiff Simulator 2008 serial key genWebcam Simulator 2.112 crackCcna Network Simulator serials keyTrainz Simulator serial makerReal Pic Simulator 1.3 patchFlightgear Flight Simulator serial makerMicrosoft Flight Simulator X Addon Fo key generatorTower Simulator-reloaded serials keySimulator Big Pack 2001.2009 keygenSpace Station Simulator 2.0 serial keygenJu-on The Grudge A Haunted House Simulator Ntsc-u key code generator6 Programme Fuer Banner, Gifs Und Bilder Zu Bearbeiten key code generatorWilli Und Die Wunder Dieser Welt Expedition 1 serial keygenLexware Faktura Und Auftrag Plus 2010 14.0 serial number makerMicrosoft Flight Simulator crackMs Train Simulator serial makerPhoenixrc Simulator Updates serial key genBus Simulator 2008 serial keygenPc/the Movies Stunts Und Spezialeffekte/addon.de.iso-ws patchMicrosoft Train Simulator Stuttgart - Muenchen serials keyUsenext Und Firstload keygenTrain Simulator - Ns Planv crackSemsim Cisco Ccna Exam Router Simulator keymakerBagger Simulator 2008 keymakerEuro Truck Simulator-reloaded Net serial key gen100 Vertragsvorlagen Und Juristische Schreiben serials key5 Progs Fuer Banner, Gifs Und Bilder serialMuellabfuhr Simulator 2008 keygenFlight Simulator 2004 serial key genFlight Simulator X Nocd serials generatorTrain Simulator serial keys genVideo2brain Calvinize I Bis Iii Beauty Retusche Und Mehr German Dvd crackTrain Simulator - Locomotives serial number makerShip Simulator patchTrain Simulator Disc 1 crackMicrosoft Train Simulator 2 serial makerFishing Simulator 2 key code generatorFlight Simulator 2002 crackRail Simulator crackTrain Simulator - Gotthard key code generatorEuro Truck Simulator 2008 serial keys genGerman Truck Simulator crackShipsim2008 Ship Simulator 2008 patchEuro Truck Simulator Pc 2008 crackMultimedia Fuehrerschein Und Ve serial makerDriving.simulator 2009 serial6 Progs Fuer Banner, Gifs Und Bilder key code generatorGerman Truck Simulator 2010 serial keygenTrainz Simulator 2009 serial number makerCondor The Competition Soaring Simulator crackMicrosoft Train Simulator-dvd.iso -lindoff.iso serial keys gen
Nothing found. Try to download Berg und Tunnelbau Simulator keygen from Media Library.

Infos for Berg-und Tunnelbau Simulator: game: Berg-und Tunnelbau Simulator BuTS Genre: Simulations: Publisher: UIG Entertainment GmbH: Release.
Jetzt anmelden und folgen Best PC V Tunnel Super Network Tunnel Tunnel Anti Filter Redirect Tunnel Proxy Berg Und Tunnelbau Simulator patch download at.